Ciphers
webPDF allows you to set the ciphers used for TLS communication.
In the default configuration, the server automatically selects the ciphers based on the set TLS and the default Java Runtime Engine.
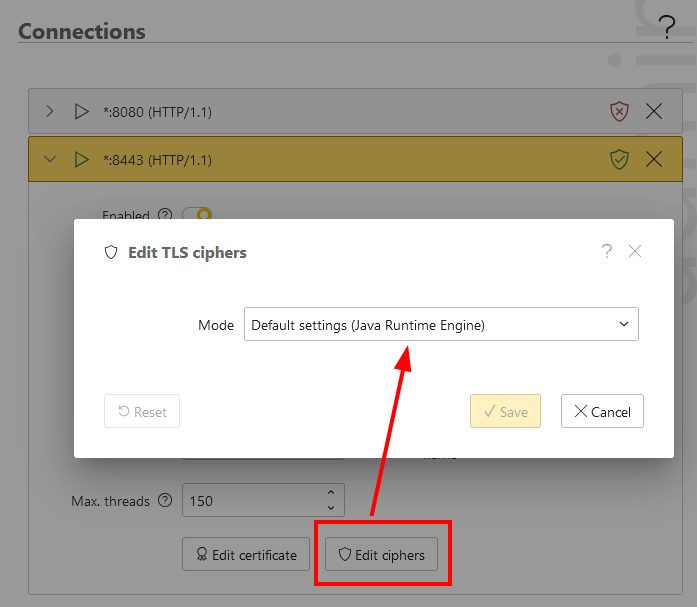
It is also possible to manually set the list of ciphers.
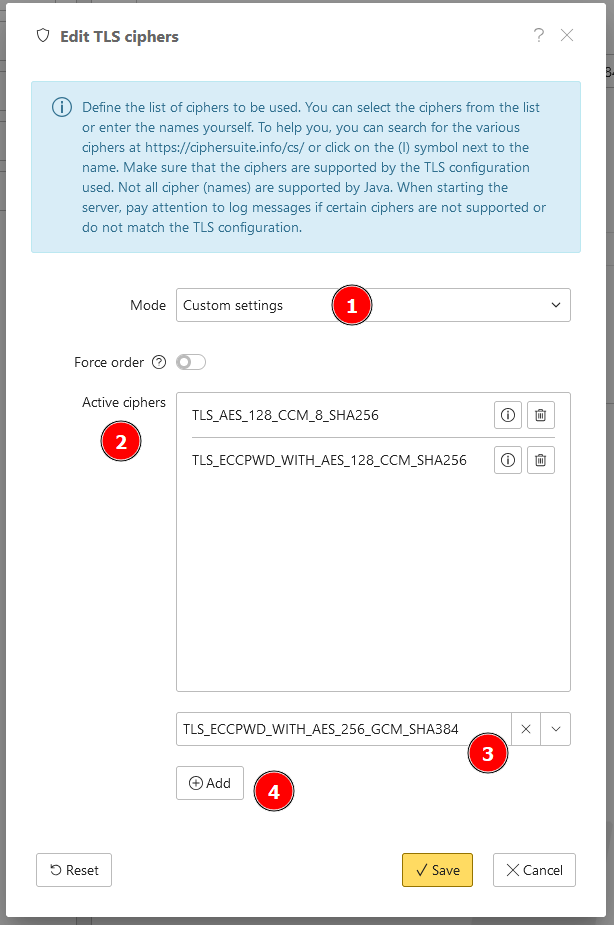
In the dialog, set the mode to “Custom settings” (1). Under “Active ciphers” (2) you will see the list of the currently selected ciphers. With the drop-down selection (3) you can select a predefined cipher or enter one manually. Click “Add” (4) to add it to the list.
At https://ciphersuite.info/cs/, you will find a list of TLS ciphers for the respective TLS protocol.
If you save the list, the server must be restarted for the configured ciphers to be activated.
The option Force order can be used to prompt the client to select the ciphers in the configured order.
Check that the selected ciphers are valid and have also been activated when starting the server. Not every cipher is available for the selected TLS protocol and Java.
Check negotiated cipher
Verify the effective cipher from a client system:
openssl s_client -connect <host>:8443 -servername <host> < /dev/null
Check the Cipher : ... line.
You can also test a specific cipher directly:
# TLS 1.2 and older
openssl s_client -connect <host>:8443 -servername <host> -tls1_2 -cipher 'ECDHE-RSA-AES128-GCM-SHA256' < /dev/null
# TLS 1.3
openssl s_client -connect <host>:8443 -servername <host> -tls1_3 -ciphersuites 'TLS_AES_128_GCM_SHA256' < /dev/null
If the handshake fails, either the cipher is not enabled in webPDF, not available in the active Java runtime, or not supported by the client.
Check cipher support and client/server matching
To troubleshoot cipher mismatches, validate all three perspectives:
- server offers
- client supports
- handshake with a specific cipher
1. Enumerate server-offered ciphers
nmap --script ssl-enum-ciphers -p 8443 <host>
This shows which ciphers are offered per TLS version and whether weak suites are still enabled.
Typical interpretation:
- only TLS 1.2 ciphers listed: TLS 1.3 is not active on this endpoint
- weak ciphers flagged by the script: server policy should be tightened
- expected cipher missing: usually filtered by TLS version, Java runtime support, or server cipher configuration
2. List client-supported ciphers
With OpenSSL (client side):
# TLS 1.2 client ciphers
openssl ciphers -v -tls1_2
# TLS 1.3 client ciphersuites
openssl ciphers -v -tls1_3
3. Prove the exact match by forcing a cipher
# TLS 1.2
openssl s_client -connect <host>:8443 -servername <host> -tls1_2 -cipher 'ECDHE-RSA-AES128-GCM-SHA256' < /dev/null
# TLS 1.3
openssl s_client -connect <host>:8443 -servername <host> -tls1_3 -ciphersuites 'TLS_AES_128_GCM_SHA256' < /dev/null
If this fails, the selected cipher is usually not available for the chosen TLS version, not offered by server policy, or not supported by the client runtime.
Always check cipher and TLS version together. A cipher name may be valid in general but invalid for the negotiated TLS protocol.
For detailed diagnosis patterns, see TLS troubleshooting.